Red Team & Pen Testing
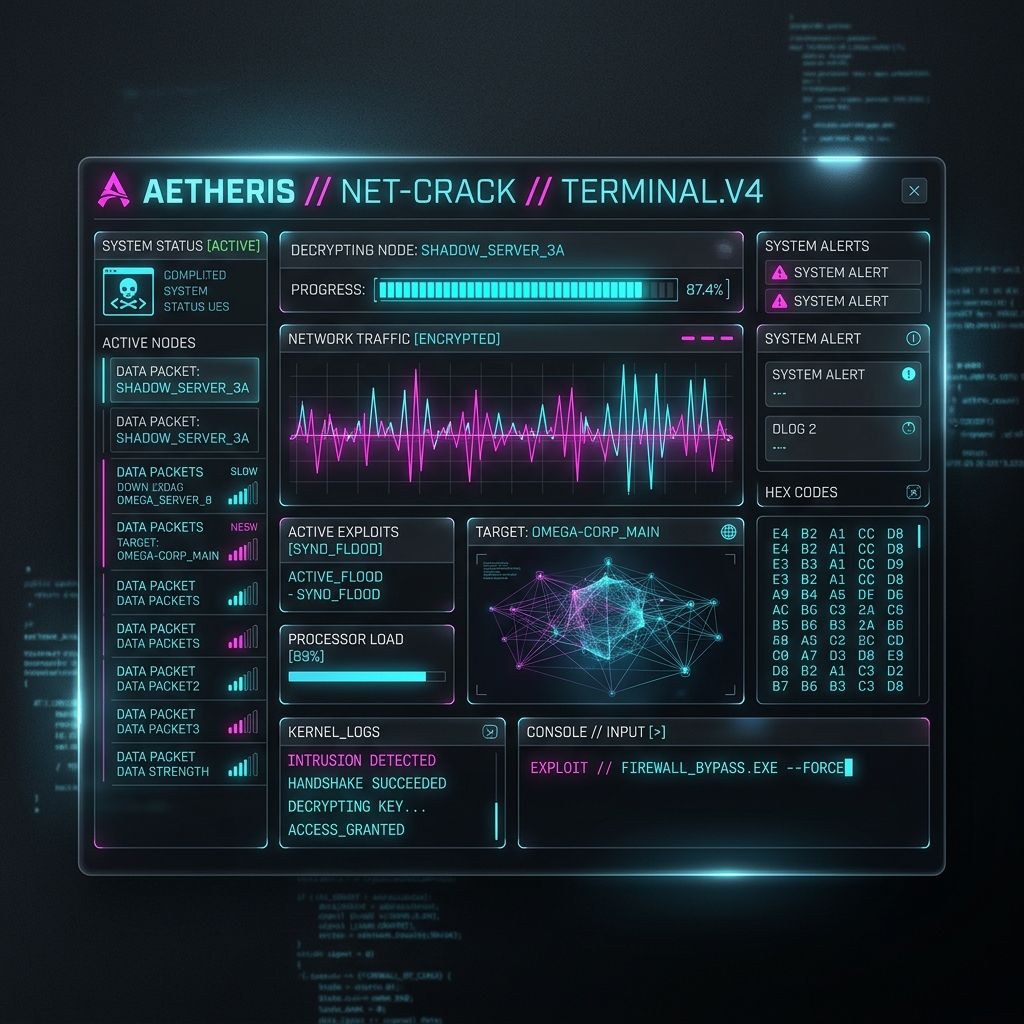
We do not rely on automated scans. Our Red Team emulates advanced persistent threats (APTs) to systematically compromise and map attack paths within your environment.
Bug Hunting & Cyber Security
Zero-day discovery and continuous infrastructure hardening. We identify logic flaws, authentication bypasses, and deeply embedded vulnerabilities before malicious actors exploit them.
Concept Thinking
Tailored cyber strategy, innovation, and risk architecture for secure digital evolution. Security shouldn't compromise usability, nor should design ignore resilience.